Everything you need to know about the Tor 2021 browser
Tor recently released a new level of security. New changes include encryption algorithms, improved authentication, and a redesigned directory system. In addition, new router domains will be longer to keep repeater addresses completely private.
Try ExpressVPN today without risk!
First about the main thing: what is Tor?
If you opened this post, you’ve probably heard of Tor and wondered if you should use it. So let’s start with the basics: so what is Tor?
Tor is an acronym for “The Onion Router”, which refers to several layers of encryption used to protect your privacy. The main feature of Tor is that it hides your footprints on the Internet, allowing you to browse the web and download anonymously.
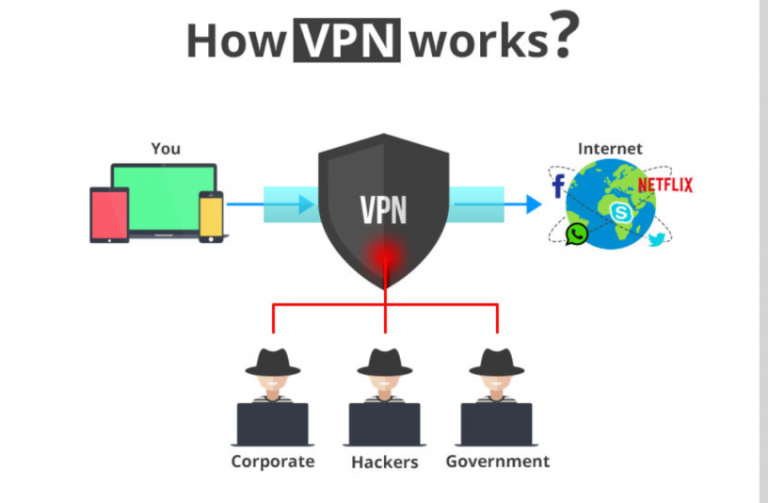
But let’s define that Tor is not a VPN service or a built-in VPN browser. Although both Tor and VPN allow private browsing, these are very different technologies.
Tor was originally developed by the US Navy to protect US communications during reconnaissance operations. It is now a non-profit organization that maintains online privacy.

How does Tor work?
Now that you know what Tor is, let’s see how it works – and how to use it.
Using Tor is relatively easy.
You simply download and install the Tor browser, which will replace Chrome, Firefox or another browser you normally use. Everything you do in Tor is private and secure.
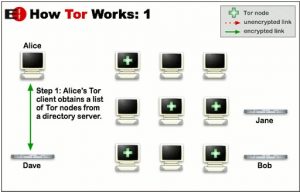
Tor puts your data in encrypted packets before it enters the network. Tor then deletes the part of the package that contains information such as source, size, destination and time, as all this data can be used to study the sender (and this is you).
Next, it encrypts the rest of the packet information before finally sending the encrypted data across different servers or changes it, randomly, so that it cannot be tracked.
Each repeater decrypts and then re-encrypts enough data to find out where it came from and where it’s going, but can’t keep track of any other information.
Many of the Tor encryption layers used for anonymity are onion-like, hence the name. The illustration below is a good (though very simplistic) explanation of how Thor works.
Why use Tor?
The Tor network hides your identity by moving your Internet activity across different Tor servers.
This allows you to have complete anonymity and security from anyone trying to track your activity, such as governments, hackers and advertisers.
Tor is also the entrance to the “Deep Network” or “Dark Network”, which sounds scarier than it really is. In fact, the Wide Web consists of most of the Internet.
Deep web consists of websites that for one reason or another are not registered in any search engine.
Although many of them were not registered by chance, some deliberately did not register because they do not want to be easily found. For example, the Silk Road, an online drug trafficking market that closed several years ago, could not be accessed by regular browsers.
A popular analogy for describing the Deep Web is an iceberg: what you can search for through standard search engines is just a clue, and the rest of the Internet or the Deep Internet is something beneath the surface.
But Tor doesn’t just support illegal activity on the Internet. It is also very popular with journalists, activists, human rights activists and informants, especially those who live or work in countries with Internet restrictions.
Thor not only hides Internet activity, but also helps circumvent censorship. For example, Edward Snowden released information through Tor.
Why not use Tor?
The biggest drawback of Tor is its performance or lack thereof.
Because data passes through many routers, Tor is very sluggish, especially for audio and video. This can make streaming video or downloading a nightmare and is one of the main reasons why more and more users are starting to use a VPN or browser with a built-in VPN.
It’s also important to know that using Tor doesn’t make you 100% invulnerable.
In fact, many people think that Tor is easy to hack because the exit nodes (the last repeater before your information reaches its destination) can see your traffic if the site you are browsing is not using SSL protocol. Using HTTPS instead of just HTTP may provide an extra layer of security, but it is still not reliable.
Finally, government agencies see if you’re using Tor, so even if they don’t see what you’re doing, it can still be a red flag for them.
Using Tor with VPN
Tor and VPN can be used in combination with each other, although their relationship is a bit complicated. You can choose Tor-Through-VPN or VPN-through-Tor, and there is a big difference between them.
We will not go into too much detail, but it is important to understand the pros and cons of each option. Also, keep in mind that no matter what setting you use, it will significantly reduce your performance.
Both Tor and VPN slow down the Internet, and the combination of the two makes it even more noticeable.
Tor-through-VPN
Tor-through-VPN has: your computer> VPN> Tor> Internet.
The advantage is that your ISP will not know that you are using Tor, even if it may still know that you are using a VPN. Also, the Tor input site will not see your IP address, which is a good extra level of security.
The downside to this setting is that your VPN knows your real IP address, and you don’t have protection against malicious Tor exit points.
Some VPN providers (such as ExpressVPN, Privatoria, and TorVPN) offer Tor-through-VPN configurations. This is fine, but nowhere will it be as secure as with the Tor browser, where Tor encryption is end-to-end.
VPN-through-Tor
The VPN-through-Tor relationship is: your computer> Tor> VPN> Internet.
VPN-through-Tor is a much more secure program, providing almost perfect anonymity.
However, this requires you to configure your VPN to work with TOR, and there are only two services we know of: AirVPN and BolehVPN.
Of course, if you don’t mind being restricted from using a particular VPN service, VPN-through-Tor is the best option.
First, the VPN service provider does not have the ability to know your real IP address, but sees the Tor output node. If you go that far, you have to pay via Bitcoin using the Tor browser, which means that the VPN provider doesn’t really have the ability to identify you, even if it keeps logs.
The next advantage is protection against malicious Tor output nodes, because your data is encrypted with VPN.
This also has the added effect of bypassing any blocks on Tor output nodes (such as censorship), which cannot be done due to VPN settings.
All this suggests that if you do not want to mess with running VPN-through-Tor, you can always run PPT using a simple Tor browser after establishing a VPN connection.
How to use Tor
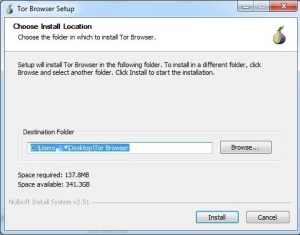
To get started, download the Tor browser, which is actually a modified version of Firefox. From here, you can apply a precautionary step to verify the signature of the package, which protects you from getting the malicious version
The next step is to install the Tor browser, which is automatically installed on your desktop.
Tor is portable software that doesn’t integrate with Windows, so you can launch the browser from anywhere on your computer, even through a USB drive.
If you want to change the location of the installation from your computer, just click the Browse button and select the desired destination from there. From now on, the installation process becomes normal.
Using Tor with a VPN or proxy
After installing the browser, a folder named “Tor Browser” will be created in the selected destination. Inside you will see “Start Tor Browser”.
When you click this, you will see the option to connect directly to the Tor network or to configure proxy settings. If you use the Vpn-through-Tor method or a proxy server (or if you are connected to a network that is controlled, censored, or restricted in any way), you will need to configure it manually using another option.
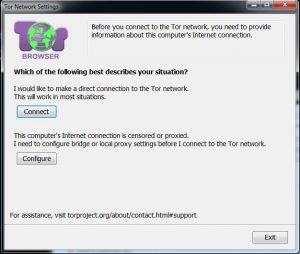
Regardless, once you’re in the Tor browser, make sure you’re connected properly by checking the IP address. If it’s not your original IP, you can get started!
When you’re online, here are some tips for extra security:
- Only go to sites that have HTTPS, but not HTTP. Although Tor encrypts all traffic on the Tor network, it does not encrypt traffic outside the network, leaving you vulnerable when your traffic reaches nodes because your data is no longer encrypted. Therefore, you should always use an encryption deadline, such as SSL or TLS, as well as sites that use HTTPS. To make sure you’re only using HTTPS sites, try using the HTTPS Everywhere plugin.
- Don’t use P2P traffic on Tor. Tor is not designed for peer-to-peer file access, and is likely to be blocked by many output nodes. Using P2P traffic on Tor threatens your online anonymity because BitTorrent clients send your IP address to the BitTorrent tracker and other programs.
- Always delete cookies – You can use add-ons, such as self-destruct cookies, to automatically delete cookies.
- Don’t use your real email address. This should be an obvious fact, but consider it a reminder. As one website stated, using real e-mail while using Tor is like “going to a masquerade ball in a suit with your name on it.”
- Don’t use Google – Google has a bad reputation for collecting information about your users’ browsing habits and search data, as they aim to increase advertising revenue. Use search engines like DuckDuckGo instead.
Concluding remarks on Tor
Personal privacy is becoming increasingly vulnerable as the government, hackers, and even our favorite Google invent more advanced ways to break your anonymity and track us. Even with its known flaws and vulnerabilities, the Tor browser is a great step towards being more anonymous online. However, this is only one part of the puzzle.
If you really want to protect yourself, consider one of the following VPN services with Tor.
Try ExpressVPN today without risk!